Table of Contents (click to expand)
A cryptophone is a mobile phone with robust security features that protect users against eavesdropping by intelligence or private organizations, and are able to avoid most surveillance measures. Cryptophones use sophisticated algorithms to encrypt the voice signals, making it difficult for intruders to break into the system and conduct surveillance.
In a recent article, we discussed the perils of a ‘dirtbox’ being used by security agencies to sniff out conversations if they deem them to be ‘suspicious’ or a threat to ‘national security’. We explained how cell phone tower emulators, e.g., StingRay, can potentially force our mobile phones to connect to it and can then extract our private and valuable data. A cryptophone is one of the shields that can protect us from the nasty prying eyes of these snooping sniffers.

Recommended Video for you:
Need For The Cryptophone
In the age of wired telephones, wiretapping was the best way to track audio communication between two parties. However, with the advent of the wireless era and consumer smartphones becoming a citizen’s essential device, there has been an explosion of new opportunities for easy snooping, as the protocols that GSM or UMTS network work on are pretty vulnerable.

And then came Edward Snowden’s revelation of how, over the course of decades, telecommunication interception has developed into a major industry. This is not just governments and their intelligence agencies, but major private organizations across the world have also been found guilty of intercepting calls that would yield them ‘economic’ or ‘business’ information. All of this is happening at the cost of our privacy.
As electronic equipment for wireless interception and tracking has dropped to a more accessible price, it is being deployed more frequently, even for comparatively small business conflicts. Using encryption as a ‘shield’ to protect your privacy is essential in this digital age.
However, protecting your information using robust encryption is not that easy. The proprietary or secret algorithms that today’s mobile and networking companies use are often found to be weak when it comes to protecting you against those who are after your data and online behavior. What’s more astonishing is that these companies use clever marketing tricks to give you a false sense of security by claiming that they are government certified—certified by the same intelligence organizations that snoop into your data in the name of ‘suspicious activity’ or ‘national security’.
Cryptophone To The Rescue
Cryptophones are mobile phones with robust security features that protect users against eavesdropping by intelligence or private organizations, and are able to avoid most surveillance measures. Unlike regular mobile phones, cryptophones aren’t black-box devices with limited technical information available to the public.

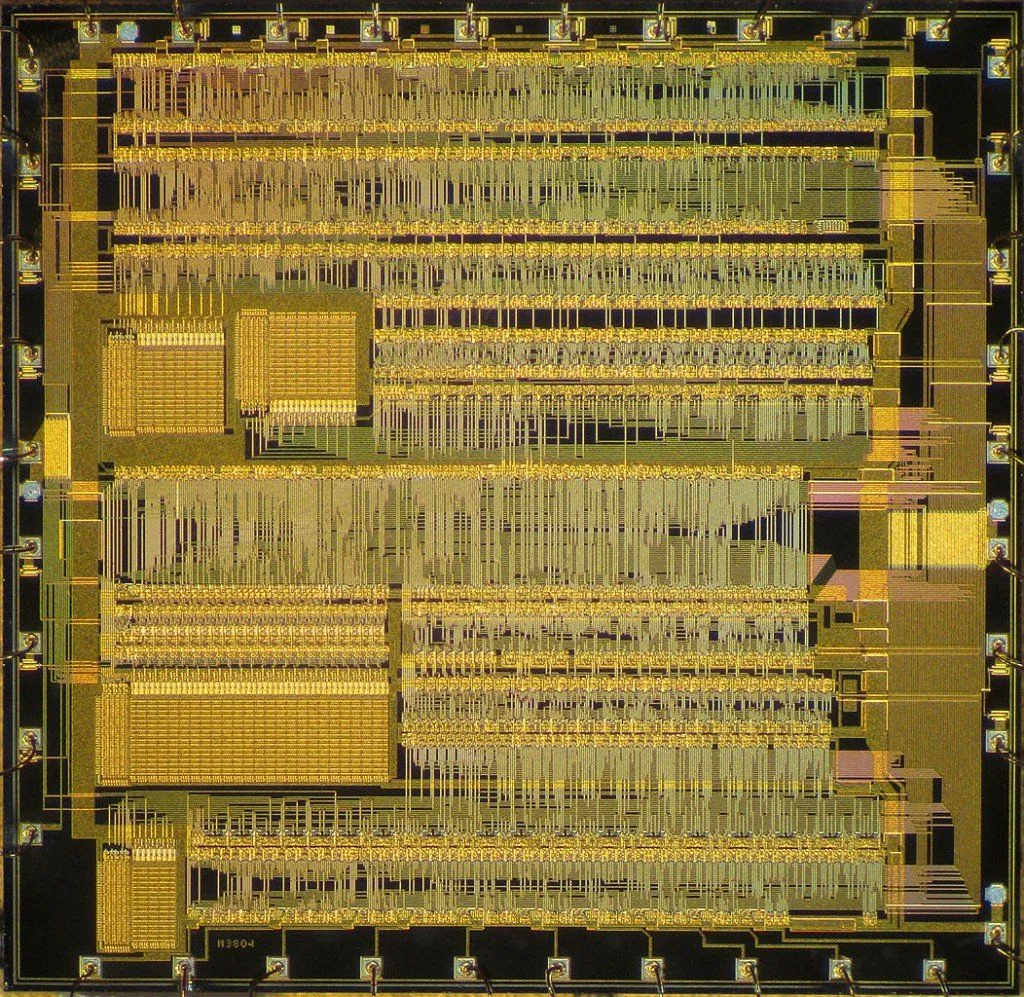
Cryptophones can avoid the interception of calls by using sophisticated algorithms to encrypt the voice signals. The heart of a cryptophone lies in its dedicated cryptographic chip, which has the power to encrypt and decrypt the signal used in communication. Two of the most secure algorithms—a key exchange algorithm and a symmetric key algorithm – are used for safeguarding audio communication between the two devices.
Now, let’s explore how cryptophones protect our privacy in more detail.
Secured Software Architecture
Cryptophones like the one from GMSK run on top of a heavily modified and stripped-down Microsoft Windows mobile operating system. GMSK believes that the Windows platform provides an affordable platform that makes it possible to deliver smooth functioning of the phone and keep tight security intact using speech encoding and crypto functions. They have stated that a Windows platform was chosen as the first cryptophone platform because it was the fastest system that allowed them to maintain software integrity protection in RAM (random access memory) and remove unnecessary functions that would hamper performance or security.
Moreover, cryptophones from GMSK come with a complete source code, which is a complete piece of operating system software.
When you observe regular mobile and telecommunication vendors, it often appears that they have something to hide. They hide their software and technical details under the guise of protecting ‘trade secrets’. Some of the manufacturers of cryptographic equipment that are also in the business of selling secure mobile phones are infamous for colluding with intelligence agencies and interested private parties. Instead of using thoroughly and rigorously tested algorithms like AES, Twofish, or Diffie-Hellman, they use ‘proprietary’ encryption methods that are hidden from the public view. Several such ‘proprietary’ encryptions, such as COMP128, were found to be easily breakable, meaning that the security of end users like us is heavily compromised. Most of the popular cryptophones on the market come with encryption technology that is academically tested and backed for usage.
Powerful Encryption Engine
Cryptophones often use the most secured and well researched encryption engines with very long keys, making it very tough for intruders to break into the system in order to conduct surveillance.
For example, cryptophones from GMSK encrypt all calls with 256-bit keys using robust AES and Twofish encryption methods. Similarly, for text messages, CCM-mode is used as a secure method for communication. General purpose phones only have one encryption method, which is often proprietary, but popular cryptophones on the market often use multiple encryption methods to provide an even stronger design. This is because, even in the highly unlikely case of breaking through one of the encryption methods, the others will provide additional layers of security. Thus, the usage of multiple encryptions provides a ‘fall back’ inside the crypto-system design. The motive behind the design of cryptophones is often far-sighted—their security is not designed to endure for a few weeks or months, but for years or even decades.
Smart Audio Compression Techniques
General purpose phones running on a GSM network come with a basic design, wherein the phone takes the voice from the microphone, digitizes it and compresses it using a compression algorithm. After that, it is encrypted and sent through a GSM data call to the other person to whom the call is intended. The compression algorithm used is typically a codec; what it does with the voice is the same as what a MP3 does with music—ensuring that it takes up less data.
Popular cryptophones, on the other hand, use two different codecs. The original cryptophone code is called CELP and runs at a frequency of 8kHz. The output stream of is 4.8kbit/second, enabling it to be transported over a 9.6kbit/sec GSM data call. The implication of this is that the speech and sound quality you can expect is comparable to international phone calls.
Some Caveats
The biggest deterrent to buying a cryptophone is the price. They are roughly 5 times more expensive than your typical iPhone. Although the pricing varies with the model and manufacturer, that is a rough price estimate. Also, you must bear in mind that to benefit from the security of cryptophones, both the conversing parties must have a cryptophone. If you call from a cryptophone to a normal mobile phone, you can’t expect the pristine security for which cryptophones were originally designed. Another problem with cryptophones is that there is some lag in the phone calls. That’s actually a side effect of the way that cryptophone communication works. Instead of placing a regular audio call, cryptophones use data bandwidth for audio communication, as this allows them to encrypt the communication using sophisticated algorithms.
Reception Of Cryptophones
With revelations from whistle-blowers like Snowden and increased awareness of the snooping on mobile networks by government and private organizations, people are looking for safe alternatives—and cryptophones provide just that. According to some estimates, there are around 100000 cryptophones on the market and demand is continually increasing, so much so that manufacturers like ESD are finding it difficult to keep up with the demand, just like Tesla cars! A few years back, after discovering bugs in his office, the prime minister of Turkey ordered cryptophones for every one of his ministers!

Cryptophones were borne from the desire to save citizens from snooping agencies. Cryptophones have robust security features, like firewalls, to identify and thwart requests from dirtboxes like StingRay. They even alert the user when a cell tower requests an IMEI capture. In this way, users have more control over what types of transmission take place between their cell phone and the cell tower, enabling them to be more protected from unsolicited attempts at interception.